vpn 部署ocserv
官方文档:https://ocserv.gitlab.io/www/index.html
原链接地址:https://www.ad7.cn/project-99/doc-280/
0-简介
Openconnect VPN服务端简称ocserv(Openconnect VPN Server),ocserv是一款开源的,兼容Cisco Anyconnect VPN的VPN服务端软件。目前状况下通讯较为稳定,干扰较小。主要优势是多平台的支持,Windows、Android、iOS都能找到它的客户端。
1-部署(脚本一部署)
1-开启防火墙
systemctl start firewalld
systemctl enable firewalld
2-运行安装脚本
【附件】ocserv-auto.zip
[root@vpn ~]# bash ocserv-auto.sh
[root@vpn ~]# bash ocserv-auto.sh
======================================
Network Interface list:
ens33
ens34
======================================
Which network interface you want to listen for ocserv?
Default network interface is ens33, let it blank to use this network interface: ens34 #选择网卡
Please input the port ocserv listen to.
Default port is 443, let it blank to use this port: #默认端口
Please input ocserv user name.
Default user name is user, let it blank to use this user name: samu #用户
Please input samu's password.
Random password is T2qdELLP0D, let it blank to use this password: samu #密码 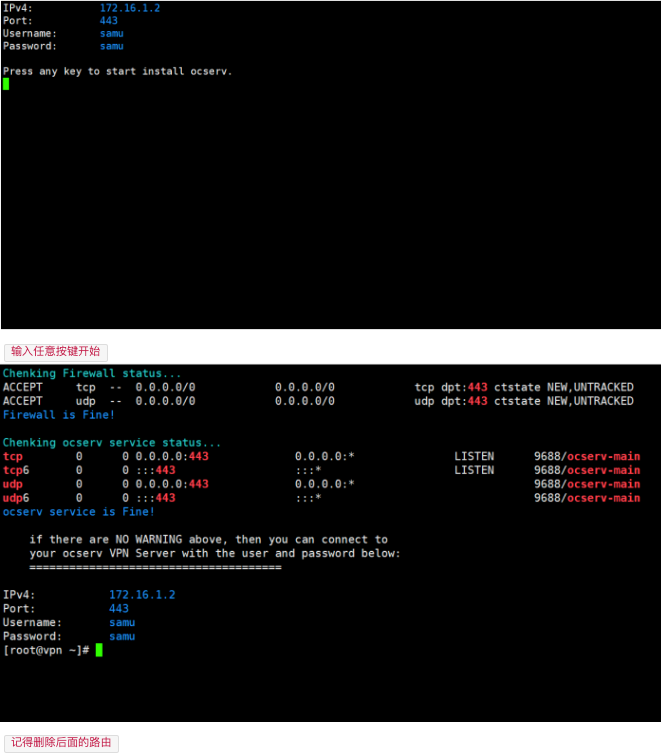
3-使用
创建用户
[root@vpn ~]# ocpasswd -c /etc/ocserv/ocpasswd user
删除用户
[root@vpn ~]# ocpasswd -c /etc/ocserv/ocpasswd -d user
启动服务
[root@vpn ~]# systemctl start ocserv
关闭服务器
[root@vpn ~]# systemctl stop ocserv
重启服务
[root@vpn ~]# systemctl restart ocserv4-测试登录
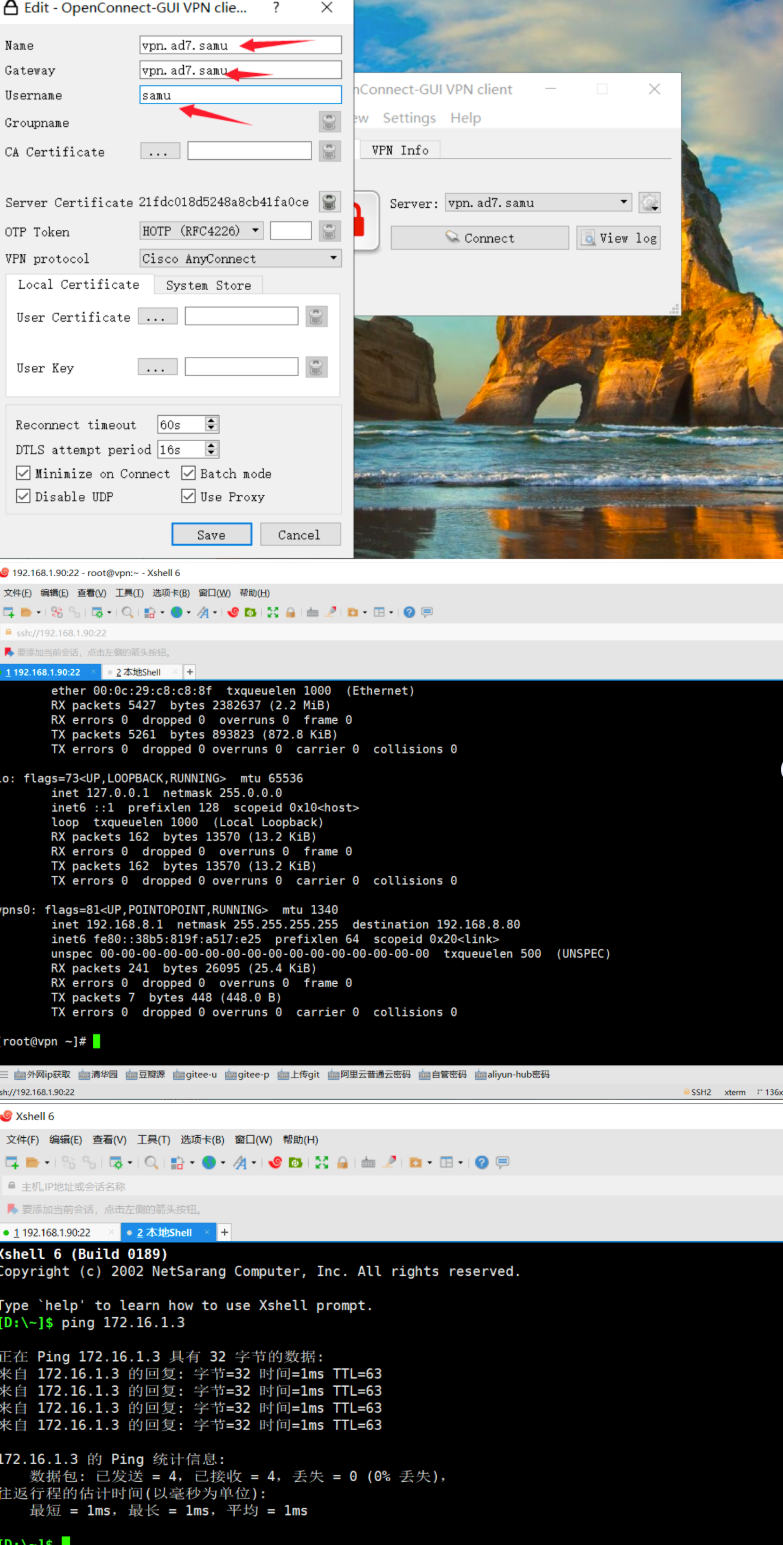
4.1-下载客户端
1.widnwos客户端
【附件】
2.安卓客户端
【附件】[[1]][anconnect]
2-测试登录
5 下载地址
[anconnect]: https://www.ad7.cn/media/attachment/2021/04/AnyConnect-4.9.06048.zip "AnyConnect-4.9.06048.zip"
[connect-windw]: https://www.ad7.cn/media/attachment/2021/04/openconnect-gui-1.5.3-win32.zip
[ocserv]: https://www.ad7.cn/media/attachment/2021/04/ocserv-auto.zip
二 ocserv-centos7 yum部署
1 ocserv 已经在 epel 仓库中提供了,所以可以直接通过 yum 安装
yum install epel-release
yum install ocserv2 创建ssl证书目录并放入证书(我证书名称ssl.pem/ssl.key)
mkdir -p /etc/ocserv/ssl
cd /etc/ocserv/ssl3 默认情况下,配置文件位于 /etc/ocserv/ocserv.conf,以下的配置字段需要重点关注
cd /etc/ocserv
mv /etc/ocserv/ocserv.conf /etc/ocserv/ocserv.conf_bak
cat << EOF > /etc/ocserv/ocserv.conf
#auth = "pam[gid-min=1000]"
auth = "plain[passwd=/etc/ocserv/ocpasswd]"
#enable-auth = gssapi[keytab=/etc/ocserv/key.tab,tgt-freshness-time=360]
#enable-auth = gssapi[keytab=/etc/ocserv/key.tab,require-local-user-map=true,tgt-freshness-time=360]
#auth = "plain[passwd=/etc/ocserv/ocpasswd]"
socket-file = /var/run/ocserv-socket
pid-file = /var/run/ocserv.pid
use-occtl = true
occtl-socket-file = /var/run/occtl.socket
#指定替代的登录方式,这里使用证书登录作为第二种登录方式
#enable-auth = "certificate"
#证书路径
server-cert = /etc/ocserv/ssl/ssl.pem
server-key = /etc/ocserv/ssl/ssl.key
#ca路径
#ca-cert = /etc/ocserv/ca-cert.pem
#从证书中提取用户名的方式,这里提取的是证书中的 CN 字段作为用户名
#cert-user-oid = 2.5.4.3
#最大用户数量
max-clients = 100
#同一个用户最多同时登陆数
max-same-clients = 1
#tcp和udp端口
tcp-port = 443
udp-port = 443
#运行用户和组
run-as-user = ocserv
run-as-group = ocserv
#虚拟设备名称
device = vpns
# 不分配固定ip
#predictable-ips = false
# mtu = 1369
#分配给VPN客户端的IP段
ipv4-network = 10.11.18.0/24
#DNS
#dns = 8.8.8.8
#dns = 8.8.4.4
tunnel-all-dns = false
#select-group = staff
#select-group = operation_cs
#select-group = coldwallet
#select-group = dev
#select-group = quant
#select-group = ops
banner = "欢迎进入xxxx内部网络"
default-select-group = staff
auto-select-group = false
#组
config-per-user = /etc/ocserv/config-per-user/
config-per-group = /etc/ocserv/config-per-group/
default-group-config = /etc/ocserv/config-per-group/test
#注释掉route的字段,这样表示所有流量都通过 VPN 发送
#no-route = 10.197.0.121/32
#r#oute = 172.31.223.184/32
restrict-user-to-routes = true
compression = true
no-compress-limit = 256
# The time (in seconds) that a client is allowed to stay connected
session-timeout = 5400
# score达到80就禁用ip, 错误密码10, kdcp 1, conncetion 1
max-ban-score = 1000
# ban重置时间
ban-reset-time = 1200
# 一次认证最长允许时间
auth-timeout = 60
# 失败后, 不能重新登录的时间
min-reauth-time = 1
# 允许的无流量时间
idle-timeout = 1800
mobile-idle-timeout = 1800
# cookie有效期
cookie-timeout = 300
persistent-cookies = true
deny-roaming = false
rekey-time = 28800
rekey-method = ssl
isolate-workers = true
# 服务器状态重置时间86400
server-stats-reset-time = 604800
keepalive = 28800
dpd = 90
mobile-dpd = 1800
tls-priorities = "NORMAL:%SERVER_PRECEDENCE:%COMPAT:-VERS-SSL3.0"
cisco-client-compat = true4 设置转发和防火墙开启端口443,设置转发
echo 1 > /proc/sys/net/ipv4/ip_forward
systemctl start firewalld.service
firewall-cmd --permanent --zone=public --add-port=443/tcp
firewall-cmd --permanent --zone=public --add-port=443/udp#### 4.1 注意这里-o的eth0为当前网卡名称
```yaml
firewall-cmd --permanent --add-masquerade
firewall-cmd --permanent --direct --passthrough ipv4 -t nat -A POSTROUTING -o eth0 -j MASQUERADE
```
#### 4.2 使配置生效
```yaml
firewall-cmd --reload
```
#### 4.3 确定没有问题之后,就可以启动 ocserv 了
```yaml
systemctl enable ocserv && systemctl start ocserv
netstat -tnlp |grep 443
```
5 设置用户 ocpasswd是存储用户密码信息
touch /etc/ocserv/ocpasswd
ocpasswd -c /etc/ocserv/ocpasswd test5.1 扩展-删除和禁用-解除禁用用户
ocpasswd -c /etc/ocserv/ocpasswd -l user1 #禁用用户
ocpasswd -c /etc/ocserv/ocpasswd -u user1 #解锁被禁用的用户
ocpasswd -c /etc/ocserv/ocpasswd -d user1 #删除用户6 occtl
occtl 是 ocserv 的管理控制工具,可以查看在线用户、ocserv 的状态等
6.1 查看在线用户
occtl show users6.2查看 ocserv 的状态
occtl show status三 配置文件详解
config-per-group = /etc/ocserv/group/
default-group-config = /etc/ocserv/group/group1 #如果创建用户的时候不分组 group1就是默认分组 用的就是group1的路由表
default-select-group = group1 #如果创建用户的时候不分组 group1就是默认分组 用的就是group1的路由表
auto-select-group = false四 问题处理
4.1 ocserv无法访问网页
参考地址:https://blog.csdn.net/lswzw/article/details/103162287
1 方法一通过firewalld转发
1.1 2张网卡。
192.168.1.10(外网)
192.168.100.1(内网,100段还有别的内网电脑。)
目的: 让100段的电脑都可以上外网通过 192.168.100.1 转发
eth0: inet 192.168.1.10/24 gateway 192.168.1.1
eth1: inet 192.168.100.1/24 no gateway1.2 开启 firewalld
systemctl start firewalld
systemctl enable firewalld1.3 开启系统转发
echo net.ipv4.ip_forward = 1 >> /etc/sysctl.conf
sysctl -p1.4 开启地址伪装
这里不开不能通过DNS。 浏览器无法使用。
firewall-cmd --add-masquerade --permanent–permanent 永久生效
1.5重新加载firewalld
firewall-cmd --reload1.6查看firewalld 信息
[root@moban ~]# firewall-cmd --list-all
public (active)
target: default
icmp-block-inversion: no
interfaces: eth0 eth1
sources:
services: dhcpv6-client ssh
ports:
protocols:
masquerade: yes
forward-ports:
sourceports:
icmp-blocks:
rich rules: 这样转发就做好了。 100网段的电脑网关设为100.1 DNS 设置为公网DNS地址就可以上网了。
2 方法二 基于iptables转发
2.1 查看防火墙
service iptables statusubuntu 下是 ufw
2.2 单台机器
iptables -t nat -A POSTROUTING -s 192.168.100.4 -j SNAT --to 192.168.1.102.3 单个子网
iptables -t nat -A POSTROUTING -s 192.168.100.0/24 -j SNAT --to 192.168.1.10五 ocserv-分组制定不同路由表
1.首先添加两个带分组的用户
ocpasswd -c /etc/ocserv/ocpasswd -g gruop1 user1
ocpasswd -c /etc/ocserv/ocpasswd -g gruop2 user22.添加创建路由表组
mkdir /etc/ocserv/group
echo -e "route = 10.10.0.0/255.255.255.0" >> /etc/ocserv/group/group1
echo -e "no-route = 211.80.0.0/255.240.0.0" >> /etc/ocserv/group/group2以上连个路由表是演示group1和group2随便写的 请自行添加路由规则
此外路由表里还可以写DNS 短线时间的参数
3.添加新的命令到ocserv.conf
config-per-group = /etc/ocserv/group/
default-group-config = /etc/ocserv/group/group1 #如果创建用户的时候不分组 group1就是默认分组 用的就是group1的路由表
default-select-group = group1 #如果创建用户的时候不分组 group1就是默认分组 用的就是group1的路由表
auto-select-group = false4 重启
/etc/init.d/ocserv stop
/etc/init.d/ocserv start自己用的配置
auth = "plain[passwd=/etc/ocserv/ocpasswd]"
# listen-host = [IP|HOSTNAME]
tcp-port = 56789
udp-port = 56789
run-as-user = nobody
run-as-group = daemon
config-per-group = /etc/ocserv/group/
default-group-config = /etc/ocserv/group/yq
default-select-group = yq
auto-select-group = false
socket-file = /var/run/ocserv-socket
server-cert = /etc/ocserv/ssl/server-cert.pem
server-key = /etc/ocserv/ssl/server-key.pem
ca-cert = /etc/ocserv/ssl/ca-cert.pem
isolate-workers = true
banner = "Welcome Banalala"
max-clients = 0
max-same-clients = 100
rate-limit-ms = 0
server-stats-reset-time = 604800
keepalive = 32400
dpd = 90
mobile-dpd = 1800
switch-to-tcp-timeout = 25
try-mtu-discovery = false
mtu=2000
tls-priorities = "NORMAL:%SERVER_PRECEDENCE:%COMPAT:-VERS-SSL3.0"
auth-timeout = 240
idle-timeout = 86400
mobile-idle-timeout = 86400
min-reauth-time = 300
max-ban-score = 80
ban-reset-time = 1200
cookie-timeout = 300
deny-roaming = true
rekey-time = 172800
rekey-method = ssl
use-occtl = true
pid-file = /var/run/ocserv.pid
net-priority = 6
device = vpns
predictable-ips = true
default-domain = example.com
ipv4-network = 10.10.0.0
ipv4-netmask = 255.255.255.0
# An alternative way of specifying the network:
#ipv4-network = 192.168.1.0/24
# The IPv6 subnet that leases will be given from.
#ipv6-network = fda9:4efe:7e3b:03ea::/48
# Specify the size of the network to provide to clients. It is
# generally recommended to provide clients with a /64 network in
# IPv6, but any subnet may be specified. To provide clients only
# with a single IP use the prefix 128.
#ipv6-subnet-prefix = 128
#ipv6-subnet-prefix = 64
#tunnel-all-dns = true
dns = 8.8.8.8
dns = 223.5.5.5
ping-leases = true
#route = 10.10.0.0/255.255.255.0
#route = 0.0.0.0/0.0.0.0
cisco-client-compat = true
dtls-legacy = true
auth = "plain[passwd=/etc/ocserv/ocpasswd]"
# listen-host = [IP|HOSTNAME]
tcp-port = 56789
udp-port = 56789
run-as-user = nobody
run-as-group = daemon
config-per-group = /etc/ocserv/group/
default-group-config = /etc/ocserv/group/yq
default-select-group = yq
auto-select-group = false
socket-file = /var/run/ocserv-socket
server-cert = /etc/ocserv/ssl/server-cert.pem
server-key = /etc/ocserv/ssl/server-key.pem
ca-cert = /etc/ocserv/ssl/ca-cert.pem
isolate-workers = true
banner = "Welcome Banalala"
max-clients = 0
max-same-clients = 100
rate-limit-ms = 0
server-stats-reset-time = 604800
keepalive = 32400
dpd = 90
mobile-dpd = 1800
switch-to-tcp-timeout = 25
try-mtu-discovery = false
mtu=2000
tls-priorities = "NORMAL:%SERVER_PRECEDENCE:%COMPAT:-VERS-SSL3.0"
auth-timeout = 240
idle-timeout = 86400
mobile-idle-timeout = 86400
min-reauth-time = 300
max-ban-score = 80
ban-reset-time = 1200
cookie-timeout = 300
deny-roaming = true
rekey-time = 172800
rekey-method = ssl
use-occtl = true
pid-file = /var/run/ocserv.pid
net-priority = 6
device = vpns
predictable-ips = true
default-domain = example.com
ipv4-network = 10.10.0.0
ipv4-netmask = 255.255.255.0
# An alternative way of specifying the network:
#ipv4-network = 192.168.1.0/24
# The IPv6 subnet that leases will be given from.
#ipv6-network = fda9:4efe:7e3b:03ea::/48
# Specify the size of the network to provide to clients. It is
# generally recommended to provide clients with a /64 network in
# IPv6, but any subnet may be specified. To provide clients only
# with a single IP use the prefix 128.
#ipv6-subnet-prefix = 128
#ipv6-subnet-prefix = 64
#tunnel-all-dns = true
dns = 8.8.8.8
dns = 223.5.5.5
ping-leases = true
#route = 10.10.0.0/255.255.255.0
#route = 0.0.0.0/0.0.0.0
cisco-client-compat = true
dtls-legacy = true- 感谢你赐予我前进的力量